Application Prompts to Elevate Security AccessOn Windows Vista and above, an application may prompt to run with full administrative privileges, despite not needing them. Thus every time the application is opened, it forces the user through a User Account Control (UAC) prompt. This also removes access to some network resources, such as mapped drives, since elevated processes run in a different context to the logged-in user. Additionally, Windows may show the program's icon with a shield: 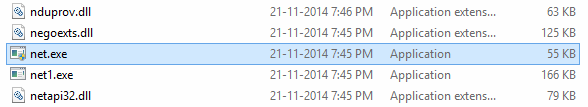 There are several ways an application can instruct Windows to prompt for administrative privileges: Shortcut PropertiesThe shortcut that runs the program, or the program file itself, may have properties set which force it to run in Compatibility Mode, or to run as an Administrator. If the shortcut (.lnk) file does not contain these settings, locate the .exe file and check the properties of that also. Manifest File- Locate the application's executable. This can be determined from the program's shortcut.
- Browse to that location.
- Locate a file in the same folder called Program.exe.manifest (where Program.exe is the name of the program's executable referenced in the shortcut). Double-click, and open with Notepad.
- Locate the section which reads:
<requestedPrivileges>
<requestedExecutionLevel
level="HighestAvailable"
uiAccess="false"/>
</requestedPrivileges> - Change “HighestAvailable” to “asInvoker”.
- Close Notepad and save the file.
An example of this usage is MYOB. AppCompatFlagsThe program can be listed under one of the following registry keys: - HKCU\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers
- HKLM\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers
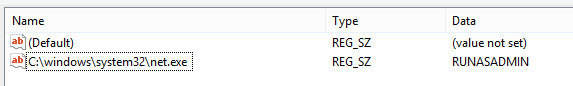 Remove the entry. |