Disabling EFS For Fun & ProfitMicrosoft Windows' whole-disk encryption system, BitLocker, was introduced with Windows Vista in 2006. But at that time, not many systems had an inbuilt TPM chip, and BitLocker was only available in Ultimate and Enterprise editions. So BitLocker was not easy to use. As of Windows 8, BitLocker was included in the mainstream Pro edition, which was the default on many systems. And as of Windows 10, a TPM chip is necessary to achieve Windows certification. So as of around 2015, BitLocker is easily used due to the software and hardware support out of the box. Prior to BitLocker, Windows 2000 introduced the encrypting file system (EFS), which enabled individual files or folders to be encrypted. In this situation, files could only be accessed by a user with the recovery certificate or the personal certificate used to encrypt them. These are not commonly backed-up, so losing the EFS certificate is a risk. Now that BitLocker is so easy to use, and EFS can be problematic if not managed, it is sometimes convenient to disable EFS so users do not inadvertently encrypt files which they later lose access to. To do this: - Open an elevated command prompt.
- Enter:
fsutil behavior set disableencryption 1 - Reboot.
Users will see the option to encrypt files/folders greyed out: 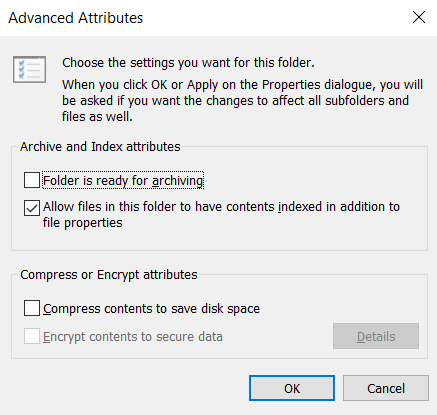 |